At the recent AIIM International AI+IM Global Summit, we asked the audience if they knew what the TWAIN Working Group does and a majority answered that they did not know, or wanted more information. So we’ve created this short explainer video as a high level overview for our 3 projects of TWAIN Classic, TWAIN Direct and PDF/Raster.
1. TWAIN Classic is a mature specification used for USB document scanners.
2. TWAIN Direct is a newer, RESTful API architecture, specification used for Ethernet or WiFi scanners and MFP’s.
3. PDF/Raster, or PDF/R, is a simplified version of PDF optimized for document scanning IoT devices.
Category: Cloud
Stargate, DeepSeek and Energy Efficiencies of AI with the TWAIN Working Group
Last week’s announcement of Stargate—a $500 billion collaboration between SoftBank, Oracle, and OpenAI—got me thinking deeply about something even more critical than the technology itself: the energy required for such massive artificial intelligence projects. This was top of mind even before this week’s announcement of DeepSeek, China’s alternative AI system, and I touched on it during the 1/24/2025 Post & Walters Ask Us Anything live podcast. When asked about my most urgent priority, I said “Energy,” and for good reason.
Oracle’s construction of massive new data centers highlights just how much space and energy these infrastructures demand. We’re now at a point where nuclear energy is being seriously considered—and in some cases, implemented—as a power source for data centers. While this level of energy use isn’t inherently bad, it raises an important question: How can we consume energy more economically and use it more efficiently?
To put this into perspective, let’s draw a parallel with the evolution of personal computers and operating systems. In the early days, when CPUs, RAM, and storage were expensive, operating system developers worked hard to optimize resource usage. However, as these components became cheaper and more abundant, efficiency often fell by the wayside, giving rise to “bloatware.” For example, the size of operating systems ballooned from Windows 3.1, which required just 6.7 MB, to modern versions occupying several gigabytes. Similar inefficiencies can be seen in software like Optical Character Recognition (OCR) tools.
Now consider Stargate, which relies on an immense data center infrastructure and consumes vast amounts of energy. Just days later, China announced DeepSeek, a competing AI system built at 1/1000th the cost ($5.6 million vs. $500 billion) and designed to use significantly less energy. According to this article, DeepSeek achieves remarkable energy efficiency, partly because sanctions on chip exports forced its creators to innovate rather than rely on resource-intensive “bloatware.” Early reviews suggest DeepSeek is an impressive competitor to ChatGPT, showing what can be achieved through intelligent, resource-conscious design.
This focus on efficiency resonates with my work on energy-conscious innovations at the TWAIN Working Group (TWG). It’s thrilling to collaborate on designing intelligent AI systems while having a meaningful, positive impact on our planet—a trifecta that aligns with my professional and personal values.
One of TWG’s key initiatives is our integration of TWAIN Direct and PDF/R technologies into RISC-V CPU chips. This enables document scanners to operate independently of external computers, reducing the need for additional CPUs, RAM, and energy. With these technologies embedded directly into IoT devices, we can develop smarter systems that consume less power. For instance, machine learning models can train in the cloud to recognize document patterns and classifications, then push those models down to the RISC-V chip for on-device classification. This approach minimizes data transmission to the cloud and enhances energy efficiency, while continuously improving through feedback loops.
Another exciting project is the addition of JPEG-XL to the PDF/R specification. Our recent white paper, “The Benefits of Adding JPEG-XL to the ISO PDF Standard and PDF/Raster,” highlights how this advanced compression format reduces file sizes, conserves storage, streamlines transmission, and encourages digital collaboration over print.
These initiatives are part of a broader strategic objective: providing secure content collaboration solutions. While this challenge might seem solved, it’s an ongoing process of innovation to combat cyber threats and ensure content authenticity, provenance, and transparency. TWG has developed reference platforms for secure documents, integrating blockchain hashing for document verification, C2PA standards for content authenticity, and advanced access controls with biometric and multifactor authentication. These solutions span various types of digital content, from photos and videos to PDF files produced by TWAIN Direct scanners.
Putting all of this together offers us all the promise that A.I. can provide, encourages safe, secure and authentic digital collaboration and, which is of great importance, converses energy so that we can all live our best lives and provide a healthy planet Earth for future generations.
With so many groundbreaking projects underway, the TWAIN Working Group and P3iD Technologies welcome anyone interested to join us. Whether you want to dip your toes in or dive in head-first, there’s a place for you in this journey of innovation.
Layering Security is easy, effective and affordable so there is no excuse for a data breach
There was a day and age not so long ago that I might have a little compassion for a data breach, but there is ABSOLUTELY no longer any excuse for these sorts of things to happen. From a technological perspective there is no reason why organizations of all sizes can’t easily implement a highly-effective, yet also affordable cyber Layer Security and Bring Your Own Security (BYOS) strategy. Below I will illustrate these layers of security with specific examples of how modern technology could possibly have greatly reduced data security risk or eliminated a data security breach altogether.
Complications of data security becomes Easier: The compassion I once had for an unintentional oversight for a data security comes from personal past experience as a network administrator when managing IT security was overwhelming complicated. IT Security was, and still is, complicated because there are so many areas of potential exposure in today’s always-on, internet-connected, reality. It’s not easy to stay informed on the rapidly evolving security technologies available these days and I can appreciate this daunting challenge.
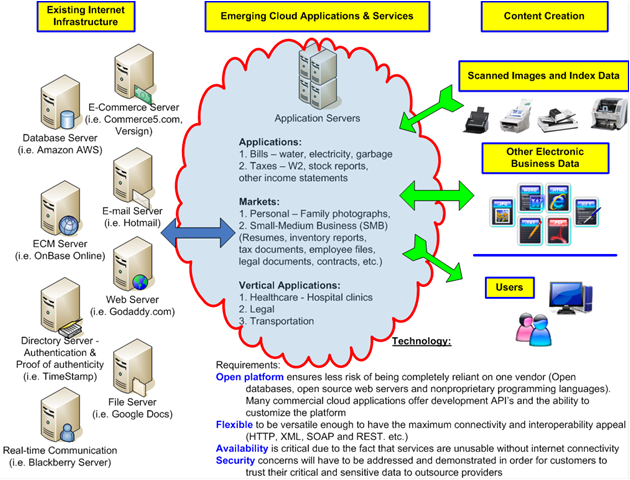
No longer should it be so complicated to implement a solid cyber security strategy with simple dashboards where administrators can easily establish, manage and control their entire multi-cloud environment, including on-premise storage, through one simple interface. The challenge of learning each individual cloud ecosystems terminology, back-end configuration as well managing user access can be delivered in a simple to understand Management Console dashboard. So ‘complicated technology’ is eliminated as any excuse for a data breach.
Laying security provides an Effective defense: Historically, there always have been silos of outstanding security products where organizations can build various layers of cyber security but these proved to be challenging for several reasons. This layering involved using different vendors which meant different business contracts with each, or it meant that each vendor was at a different phase of their product life-cycles or the interoperability between the systems wasn’t smooth or flaky at best.
However, using modern and innovative security solutions that are tightly integrated with many layers of security methods — bordering on the verge of ‘paranoid’ levels — makes it much easier for network administrators to address many of these areas of data exposure risks. Nowadays implementing a fully integrated, end-to-end IoT security layered platform from device to storage literally takes only minutes. This Security-as-a-Service technology leaves all the magic of these secure layers to the back-end system automation where the administrators or users themselves never have to get involved. This highest level of security paranoia just simply happens without worry so providing a fully layered security stack of technology. No longer is there any excuse for a data breach because these layers do not consist of many disconnected parts; it’s simply one secure IoT platform.
Enterprise Security commoditized and now Affordable for everyone: ‘The Cloud’ has, unquestionably, delivered on the great promise of bringing technology and services which were once only affordable to large enterprise customers and now to organizations of all sizes. This is a shared cost of the cloud economy business model. For example, Salesforce delivers enterprise level CRM services, Amazon delivers enterprise Web Services (AWS) infrastructure and Google provides enterprise class business applications, all at great scale and with the highest levels of reliability. The common denominator where these companies can offer such enterprise services at such affordable costs is that ‘the cloud’ allows everyone to share in the costs, yet also share in the benefits. The same concept of offering enterprise grade salesforce automation, infrastructure services and business applications can now be applied to an Enterprise Data Security strategy which is affordable for everyone. For this reason, that traditionally enterprise class security was only available to organizations with large spending budgets is absolutely not an excuse for a data breach.
Now that we’ve taken a look at three factors which eliminate any excuse for a potential data breach, let’s take a look at each layer in a bit more detail and cite a recent example.
- Bring your Own, always-on, data Encryption
Data breaches are not always the result of some nefarious black-hat hacker trying to steal your most sensitive corporate data. Sometimes honest mistakes happen such as is the case where the Pentagon exposed some of its data on Amazon server(1). This is an example where the complications of a Data Security implementation were overlooked or ignored. In this particular case anyone that had an Amazon Web Services account had access to the data stored because of a misconfiguration. It’s not that the technology wouldn’t have worked but there are just simply too many honest ways to misconfigure security settings.
This would not have happened if the Pentagon had implemented encryption security that wasn’t tied exclusively with Amazon’s Web Service user accounts and brought their own data encryption technology while still using the exact same Amazon S3 storage system they are currently utilize so no change in workflow. They could just have automatically enforced an encrypted secure strategy with technology that is not optional, it’s always-on as a default and cannot be misconfigured.
- Virtual, non-Physical, Key Encryption System
Another example of most likely an honest mistake is where Uber Got Hacked Because It Left Its Security Key Out In Public(2) and the consequences are wide ranging where now Uber Is Already Getting Sued Over Its Gigantic Data Breach.(3) In this particular situation the traditional approach of using password security ‘keys’ led directly to a ransom demand, and consequent payment, to a nefarious hacker. Using traditional security key management methodology, password ‘keys’ are similar to a username/password combination or a physical software ‘key’ file that locks (encrypts) and unlocks (decrypts) files or your car door. The risk is that with a physical asset and storing ‘keys’ in this manner, there exists the possibility of exposure no matter how safe an organization attempts to store these keys. It’s like if you left the keys to your front door on the front porch of your home.
With a modern, cloud-first, approach there would be no physical key to compromise, and thus further reduce risk data breach exposure. While keys are still necessary to encrypt and decrypt files, the idea of physical keys should be a thing of the past. Ideally the keys should be only temporary used in memory and then instantly destroyed when not needed. This is the best approach available and can be achieved when people seriously consider new types of innovation instead of the standard ‘herd mentality’ by just continuing to do things as they’ve always been done. The golden rule should be that you can’t break what’s not there.
- Biometrics Multi-Factor Authentication
Other times the technology itself exposes risks as was the case with Western Digital (WD) where it was suggested from SEC Consult Vulnerability Lab as a Top tip: Unplug your WD My Cloud boxen – now(4). Western Digital provides network-attached storage (NAS) solutions and an easy way to use these WD devices is through a web interface. In this particular breach it was verified that there is a known vulnerability where hackers can bypass username/password authentication and get direct access to the root file system and all the data stored on these NAS devices.
Nowadays nearly all mobile phones and even computers have cameras and microphones. Facial and Voice Recognition are becoming more mainstream with the likes of Amazon Alexa, Google Voice and Microsoft Cortana and technology exists where users can easily register their face and/or voice as another form of user authentication. In this case, a second form of authentication, instead of just only username/password authentication, such as Face or Voice would have prevented unauthorized access to the data on these devices. Also, while passwords might be easily guessed if not using a strong password, face and voice is much harder to duplicate. Today’s modern technology can allow a user to register their Face or Voice in just a few minutes and further reduce the risk of a potential data breach with this multi-factor authentication approach to an overall cyber security strategy.
- Strip files of their digital identity and store in a manner safe even when stolen
Lastly, when all else fails, such as where Oxford and Cambridge Club data breach: 5,000 members’ data compromised after backup hard drive stolen(5) then you have to be assured that these nefarious hackers can’t understand your data even when they are in physical possession of the content. Just assume an absolute worst-case scenario where (a) multi-factor authentication was circumvented, (b) unauthorized data decryption was achieved with brute force and (c) the hacker was in physical possession of your content where you can’t erase or take any counter-measures. In this case you certainly don’t want your files to appear as recognizable files such as a PDF medical record, a legal agreement document or a financial spreadsheet.
So how can you achieve this? Using innovative security technology, you would strip these PDF, DOCX or XLXS files of their digital identity, meaning absolutely no metadata about the objects themselves is available to the hacker. No obvious file extensions such as ‘.pdf’ are ever exposed. Then filenames themselves are cleansed of their real name such as ‘credit card numbers.xls’ and each object is split into completely random folders/sub-folders and files which render these items completely unusable to the hackers. In fact, to ensure a security level past the paranoid level a single object can be striped across multiple backend storage systems to provide a true hybrid storage solution.
In summary, I hope that you can appreciate that implementing an innovative, modern, cloud-first, Bring Your Own Security (BYOS) data security strategy provides no excuse for breaches. In a perfect world a combination of all the above layers of security which fits seamlessly into existing user workflows, that is easy to implement from a technical perspective and is affordable to everyone is cyber security euphoria.
I would not want to be the next person or organization that has to deal with one of these security breaches when the technology is available to avoid such disaster. There are two distinctly different ROI’s from my perspective. The obvious ROI is ‘Return on Investment’ by using technology to improve business process to enhance productivity, decrease operational costs and create a competitive advantage which is rather easy to measure. And then there is the second, not so obvious ROI, which is reduced ‘Risk of Investigation’ through a lax data security strategy. I just wish during my personal experience as a network administrator that the technology existed which would provide the maximum ROI to both extremes. The bottom line is that a sound cyber security strategy is the responsibility of everyone in an organization from CEO, CFO, CIO, CTO, employees to partners and providers so everyone must careful consider and participate in securing data. There is simply no excuse for a data breach.
References:
1. Pentagon exposed some of its data on Amazon server
2. Uber Got Hacked Because It Left Its Security Key Out In Public
3. Uber Is Already Getting Sued Over Its Gigantic Data Breach
“Uber failed to implement and maintain reasonable security procedures and practices appropriate to the nature and scope of the information compromised in the data breach,”
4. Top tip: Unplug your WD My Cloud boxen – now
5. Oxford and Cambridge Club data breach: 5,000 members’ data compromised after backup hard drive stolen
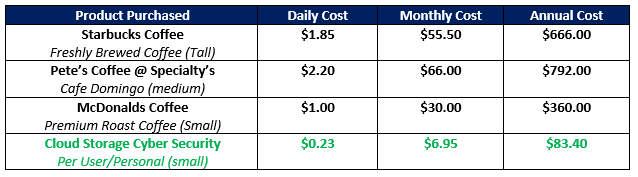
Cloud Storage Cyber Security for the price of a Cup of Coffee
Do you think that having an enterprise-grade cloud storage cyber security system is expensive? Think again because this level of access to some of the most sophisticated cyber security technology can cost less than a cup of Coffee.
Like most of you when I hear such a claim of incredible availability to a product or service for this sort of an unbelievable affordable cost, I would naturally be suspicious. For this reason, in this article, I would like to explain the business economics of why this is possible and realistic. It is amazing, yet absolutely true, that organizations of all sizes can now implement a comprehensive cloud storage security solution so affordably.
IoT Endpoint Protection:
- Application interface costs drastically decreased: One of the first costly challenges for cloud storage security is something rather easy to understand and this is how to ensure that each endpoint is secure. By endpoint this simply means devices at the front-end of a network that initially consume data to back-end devices of a network that store the data, or each ‘end’ for creating, storing and utilizing information. Therefore, you would look for one solution that is truly ubiquitous and can run on all devices including iOS and Android mobile devices and all flavors of operating systems including Windows, Linux and Mac via a web browser that is universally supported. When one solution supports all these endpoints then there is no additional development efforts required.
- Bring Your Own Security to commoditized cloud storage: Another way that cloud storage security can be highly effective, yet still affordable is using a Bring Your Own Security (BYOS) strategy to commoditized cloud storage. Cloud Storage providers such as Amazon, Google, Oracle, IBM, Alibaba and others have built massive cloud storage infrastructure and are competing like crazy for market share so why not take advantage of this competition to your advantage? Now you can by bringing several key security functions including a Unified Virtual Key Encryption strategy, File Obfuscation and physical file segregation at the individual object level among these Multi-Cloud Repositories. This affords organizations of all sizes the mutual benefit of getting massive amounts of cloud storage from any one, or all of these providers, and also the benefit to easily apply your own enterprise-grade cloud security policy across these different storage vendors.
Security-as-a-Service:
- Reduced price through a shared costs business model: Just like the cloud storage providers can offer these incredible amounts of storage space at such an affordable cost, cloud storage cyber security can now be offered in the same manner. Everyone participates in the costs of on-going product development, maintenance and supporting the infrastructure through a software subscription monetization model. This financial arrangement is analogous to some high budget movie that costs millions of dollars to produce, distribute and promote. There is no way in the world that one person would pay millions of dollars to watch this movie, but since this is a shared expense among many people through the purchase of movie tickets then it affords everyone the opportunity to see this blockbuster film but at an affordable cost shared by all.
- No dedicated labor expense for technical resources: Long gone are the days of complicated cyber security technologies that require dedicated technical resources to install, configure and manage. In today’s modern age of cloud cyber security computing, organizations just simply subscribe to a service and literally, in minutes, can be utilizing these secure hybrid cloud storage capabilities. With Simplified Management Consoles that are easy to understand it does not take software engineers or years of technical training to manage these systems. When changes or modifications are required to the security system such as adding/removing users, adding/modifying additional storage or providing sharing folder/file permissions then these systems can be easily operated by a knowledge work that needs no specific training on the nuances of cyber security, yet still ensure no bad unintentional consequences.
Roadmap Flexibility and Scalability:
- Reduced liability risk and simplified compliance/regulation: The intangible costs of decreasing risk are something rather difficult to measure yet this has to certainly considered when an organization takes into account all aspects of the business. It’s well-known that the costs of attorneys, lawyers and going through an eDiscovery process associated with lawsuits over data breaches is expensive and has driven, or will drive, breached companies out of business forever. This is a real-world fact. So, having a solid cyber security IoT Endpoint technology with many layers of defense that rivals true cyber breach paranoia, greatly helps with audits and risk compliance. This layered security is not simply a checkbox on an audit survey, but real, defendable methodology that can assist if justifying risk reduction of data breaches. One excellent example is deploying a Universal Virtual Key Encryption system which eliminates physical encryption keys. If they simply don’t exist then they can not be compromised. This one example using a new approach to Key Management can save organizations hundreds of thousands, or millions, of dollars expense for the technology itself as well as the labor safe guards for physical keys.
- Tremendous costs savings affords for more functionality: Over time, the total savings of a BYOS strategy for a multi-cloud environment really begins to make such a positive impact to the financial bottom line that organizations consider re-investing some of these savings. Since these savings were a direct result of a solid cloud storage security strategy then the obvious area of added functionality is to even further enhance the overall cyber security portfolio through complimentary capability such as Endpoint Detection and Response (EDR). By investing in EDR portfolio capability such as real-time dashboard analytics, proactive responses/alerts and actions or intrusion monitoring then powerful insights can be gleaned to further enhance the business process, certainly from a security perspective, but also to enhance an organizations worker productivity.
In summary, coffee is great and I’m not advocating abandoning your morning cup of java if that helps you get going in the morning. I just use this reference to illustrate the fact that to implement an enterprise-grade cloud storage cyber security solution is not only highly effective, but also extremely affordable at only pennies per day. Is your data security worth only a fraction of a Cup of Coffee?
Picture courtesy of OddTodd.com. OddTodd is a humorous website about a cartoonist guy named Todd that was once laid-off and then parlayed his funny character and cartoon skills into a successful career. OddTodd really likes his Coff-ay too!
Kevin Neal Life Update, 10/30/2017
 Since the end of last month when I sustained my ankle injury, life has been challenging. While I’m very grateful and fortunate because the injury could have been so much more worse, the truth of the matter is that I’m not a very patient person and the disruption to my normal routine has been difficult, to say the least.
Since the end of last month when I sustained my ankle injury, life has been challenging. While I’m very grateful and fortunate because the injury could have been so much more worse, the truth of the matter is that I’m not a very patient person and the disruption to my normal routine has been difficult, to say the least.
I’m very fired up for this upcoming week! Let me start with the highlights first.
I have taken my downtime over the past few days, and weeks, to organize some meetings that I am so much looking forward to this week. Some of these meetings are professional but some are also very personal. I’m looking forward to each of them with equal excitement, yet for extremely different reasons. Most of all I’m so pleased that Brandee will participate in each of them.
 Whether by fate, destiny or divine intervention, I have had to lean on Brandee for so many things due to my ankle injury last month. Right now, I cannot do many of the normal things I used to do. Or even if I can do them, it’s at a much slower pace than usual. She just has this uncanny ability to jump right in and get things done without me even asking, or realizing that I needed help in the first place.
Whether by fate, destiny or divine intervention, I have had to lean on Brandee for so many things due to my ankle injury last month. Right now, I cannot do many of the normal things I used to do. Or even if I can do them, it’s at a much slower pace than usual. She just has this uncanny ability to jump right in and get things done without me even asking, or realizing that I needed help in the first place.
In addition to our meetings this week I’ve been doing a lot of educating myself in various disciplines. I’ve always felt that my professional business value, to be very honest, is not that I am necessarily an expert at any one thing in particular. Rather I have a well-rounded professional background where I can relate to others in a sincere manner. I have professional experience in sales, marketing, customer service, business management, account management, product management, technical and other skills rather than just one particular job responsibility throughout my business career. I have
been very fortunate for this and I’ll never forget some very wise advice Dave Wood gave me many, many years ago. He said, “Kevin, even if you continue working at the same Company, do something different within the company.” I could not agree any more strongly than I could with this great advice from such a terrific person as Dave.

An area of particular focus recently has been digging deep into the setup, configuration and usage of ‘cloud services’. This is a very daunting task as the information is overwhelming, the terminology and services offered are different for each provider and the learning is typically on-your-own instead of some formal classroom style course. This is good and bad. It’s good because you can move at your own pace, which I’m finding really beneficial. However, the learning-curve just to get started is a bit overwhelming. Overall, technology is something I’ve always been interested in so my thirst to learn is genuine and natural. I’m glad I can apply this to my professional career. This learning I’ve been doing recently should be of great benefit to myself, but most important our partners and clients, in this current era of technology convergence between traditional/on-premise and cloud computing services.
Another thing that has me really fired up is that after several weeks of uncertainty with not knowing about my mobility (or ability to work at all), having to juggle my calendar to re-schedule so many planned activities and having to level-set my personal business strategy; for the first time in weeks, I feel that I have a solid schedule to follow this week. I spent the end of last week, as well as this past weekend, preparing a lot of documentation and discussion materials that should be very useful in our upcoming business meetings this week to have positive and productive outcomes.
 Lastly, and most importantly, and I’ll say it once again, I am so grateful for the compassion and kindness of all of you. I have such incredible faith in the decency of humanity. So many of you have been so incredibly supportive of Brandee and I dealing with my injury that we cannot thank you enough. Your kind words, thoughts and prayers are absolutely felt and appreciated. We can only hope to do what little we can to reciprocate for you and your family in some fashion, manner or capacity. At certain times in life you must slow down, reflect, appreciate, regroup and then move-forward, stronger and better than ever.
Lastly, and most importantly, and I’ll say it once again, I am so grateful for the compassion and kindness of all of you. I have such incredible faith in the decency of humanity. So many of you have been so incredibly supportive of Brandee and I dealing with my injury that we cannot thank you enough. Your kind words, thoughts and prayers are absolutely felt and appreciated. We can only hope to do what little we can to reciprocate for you and your family in some fashion, manner or capacity. At certain times in life you must slow down, reflect, appreciate, regroup and then move-forward, stronger and better than ever.
When life gives you lemons, make lemonade!