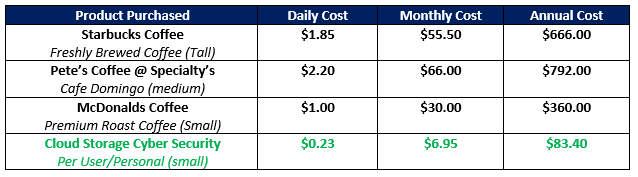
Do you think that having an enterprise-grade cloud storage cyber security system is expensive? Think again because this level of access to some of the most sophisticated cyber security technology can cost less than a cup of Coffee.
Like most of you when I hear such a claim of incredible availability to a product or service for this sort of an unbelievable affordable cost, I would naturally be suspicious. For this reason, in this article, I would like to explain the business economics of why this is possible and realistic. It is amazing, yet absolutely true, that organizations of all sizes can now implement a comprehensive cloud storage security solution so affordably.
IoT Endpoint Protection:
- Application interface costs drastically decreased: One of the first costly challenges for cloud storage security is something rather easy to understand and this is how to ensure that each endpoint is secure. By endpoint this simply means devices at the front-end of a network that initially consume data to back-end devices of a network that store the data, or each ‘end’ for creating, storing and utilizing information. Therefore, you would look for one solution that is truly ubiquitous and can run on all devices including iOS and Android mobile devices and all flavors of operating systems including Windows, Linux and Mac via a web browser that is universally supported. When one solution supports all these endpoints then there is no additional development efforts required.
- Bring Your Own Security to commoditized cloud storage: Another way that cloud storage security can be highly effective, yet still affordable is using a Bring Your Own Security (BYOS) strategy to commoditized cloud storage. Cloud Storage providers such as Amazon, Google, Oracle, IBM, Alibaba and others have built massive cloud storage infrastructure and are competing like crazy for market share so why not take advantage of this competition to your advantage? Now you can by bringing several key security functions including a Unified Virtual Key Encryption strategy, File Obfuscation and physical file segregation at the individual object level among these Multi-Cloud Repositories. This affords organizations of all sizes the mutual benefit of getting massive amounts of cloud storage from any one, or all of these providers, and also the benefit to easily apply your own enterprise-grade cloud security policy across these different storage vendors.
Security-as-a-Service:
- Reduced price through a shared costs business model: Just like the cloud storage providers can offer these incredible amounts of storage space at such an affordable cost, cloud storage cyber security can now be offered in the same manner. Everyone participates in the costs of on-going product development, maintenance and supporting the infrastructure through a software subscription monetization model. This financial arrangement is analogous to some high budget movie that costs millions of dollars to produce, distribute and promote. There is no way in the world that one person would pay millions of dollars to watch this movie, but since this is a shared expense among many people through the purchase of movie tickets then it affords everyone the opportunity to see this blockbuster film but at an affordable cost shared by all.
- No dedicated labor expense for technical resources: Long gone are the days of complicated cyber security technologies that require dedicated technical resources to install, configure and manage. In today’s modern age of cloud cyber security computing, organizations just simply subscribe to a service and literally, in minutes, can be utilizing these secure hybrid cloud storage capabilities. With Simplified Management Consoles that are easy to understand it does not take software engineers or years of technical training to manage these systems. When changes or modifications are required to the security system such as adding/removing users, adding/modifying additional storage or providing sharing folder/file permissions then these systems can be easily operated by a knowledge work that needs no specific training on the nuances of cyber security, yet still ensure no bad unintentional consequences.
Roadmap Flexibility and Scalability:
- Reduced liability risk and simplified compliance/regulation: The intangible costs of decreasing risk are something rather difficult to measure yet this has to certainly considered when an organization takes into account all aspects of the business. It’s well-known that the costs of attorneys, lawyers and going through an eDiscovery process associated with lawsuits over data breaches is expensive and has driven, or will drive, breached companies out of business forever. This is a real-world fact. So, having a solid cyber security IoT Endpoint technology with many layers of defense that rivals true cyber breach paranoia, greatly helps with audits and risk compliance. This layered security is not simply a checkbox on an audit survey, but real, defendable methodology that can assist if justifying risk reduction of data breaches. One excellent example is deploying a Universal Virtual Key Encryption system which eliminates physical encryption keys. If they simply don’t exist then they can not be compromised. This one example using a new approach to Key Management can save organizations hundreds of thousands, or millions, of dollars expense for the technology itself as well as the labor safe guards for physical keys.
- Tremendous costs savings affords for more functionality: Over time, the total savings of a BYOS strategy for a multi-cloud environment really begins to make such a positive impact to the financial bottom line that organizations consider re-investing some of these savings. Since these savings were a direct result of a solid cloud storage security strategy then the obvious area of added functionality is to even further enhance the overall cyber security portfolio through complimentary capability such as Endpoint Detection and Response (EDR). By investing in EDR portfolio capability such as real-time dashboard analytics, proactive responses/alerts and actions or intrusion monitoring then powerful insights can be gleaned to further enhance the business process, certainly from a security perspective, but also to enhance an organizations worker productivity.
In summary, coffee is great and I’m not advocating abandoning your morning cup of java if that helps you get going in the morning. I just use this reference to illustrate the fact that to implement an enterprise-grade cloud storage cyber security solution is not only highly effective, but also extremely affordable at only pennies per day. Is your data security worth only a fraction of a Cup of Coffee?
Picture courtesy of OddTodd.com. OddTodd is a humorous website about a cartoonist guy named Todd that was once laid-off and then parlayed his funny character and cartoon skills into a successful career. OddTodd really likes his Coff-ay too!